Spam protection, AntiSpam, FireWall by CleanTalk, a newly discovered vulnerability in WordPress. This SQL vulnerability is capable of exposing user emails, passwords and payment information to bad actors.
Plugins by CleanTalk has been installed on more than 100,000 websites and was intended to safely remove and reject spam and trash comments.
How it works:
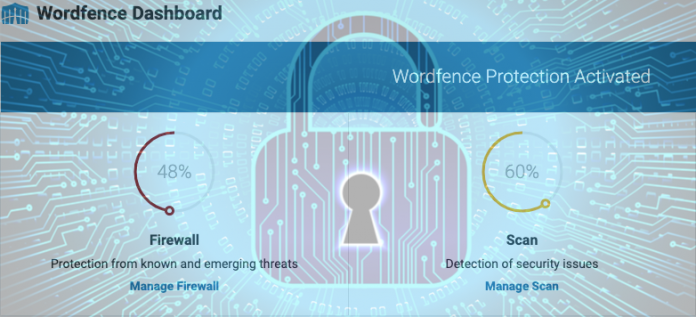
According to WordFence, the program detects, monitors and tracks activities and behavior of different IP addresses. This process of protection also applies to the user-agent string that browsers release to identify themselves as a safe source.
The firm that released the analysis on Tuesday mentioned, “Unfortunately, the update_log function in lib/Cleantalk/ApbctWP/Firewall/SFW.php, which was used to insert records of these requests into the database, failed to use a prepared SQL statement.”
Attackers can interfere with the queries made by applications, simply by taking advantage of the SQL-injection which is recognized as a web-security vulnerability.
How it can be prevented:
One of the most prominent ways of preventing this vulnerability from affecting the systems is to use “prepared statements”.
Prepared statements are pre-generated scripts that act as an isolation filter so that the attackers don’t see the entire scope of data that is returned when a query is made.
WordFence was able to present some features in the plugin code that would prevent issues from arising and make sites difficult to exploit. For example, WordFence stated that the vulnerable SQL query is an “insert” query.
“Since data was not being inserted into a sensitive table, the insert query could not be used by an attacker to exploit the site by changing values in the database, and this also made it difficult to retrieve any sensitive data from the database,” according to Wordfence.
A new patched version of the plugin is now available and all admins are advised to update to the new version – 5.153.4.